Industrial inspection robots are mobile data-gathering systems: they carry measurement sensors and are designed to navigate facilities built for humans. The usage of this technology is rapidly growing, yet comparing different robotic inspection offerings can be overwhelming. It involves knowing why you require the technology, considering the suitability of an entire solution, i.e., looking beyond the physical robotic carrier platform, evaluating the solution from an end-to-end perspective, and ultimately partnering with an enterprise-level vendor.
If you are interested in using ground robots to automate industrial inspection jobs in your plant operations, this three-part article series is for you:
- Identify the task you want to automate
- Find the right inspection robots for your facilities
-
Ensure data integration and safety features
They will equip you to evaluate different platforms, understand the industrial inspection ecosystem, and make informed decisions around requirements, applications, and suitability.
This article focuses on the last steps in evaluating inspection solutions: data integration and safety
Table of contents:

The Importance of Integration and Safety Features in Inspection Robots
In the selection process of inspection robots for industrial applications, besides understanding which task you want to automate and which is the best solution for your industrial environment, it is essential to thoroughly assess two critical aspects: integration with existing data management systems and the presence of safety features.
The seamless integration of inspection robots with pre-existing data management infrastructure ensures efficient data handling, analysis, and storage. This integration enables streamlined workflows and facilitates access to historical data, enhancing decision-making processes and enabling proactive maintenance strategies.
Simultaneously, evaluating the safety features of inspection robots is paramount to safeguarding both human operators and valuable assets. Features such as collision avoidance, emergency stop mechanisms, and fail-safe protocols mitigate the risk of accidents or damage during inspection operations.
By prioritizing integration capabilities and safety features, businesses can maximize the effectiveness and safety of their inspection processes, ultimately optimizing productivity and minimizing downtime.
Prioritize Data Integration Aspects
Robots add maximal value when they are integrated into existing operations. When fully integrated, robotic inspection is seamlessly connected to your plant’s operations management systems and requires no manual data processing steps. It also means that non-robot experts can operate the robots, which requires high ease of use.
During the qualification of vendors, it’s important to pay close attention to the robot’s capabilities related to data collection and analysis to ensure optimal performance and decision-making. While some solutions are turnkey and can be deployed quickly, others require the overhead of working with third-party payload or software providers.
Here are some points you might consider when evaluating inspection robots:
Inspection robots and data integration
- Digital Twins integration
Your business may already have created digital twins of its facilities. In this case, choosing a robot that can integrate with the existing work, leverage and update existing digital twins, or create new ones is essential.
If you don’t have an existing digital twin, consider an inspection solution that can easily create one. This choice can significantly enhance the impact and value of using it. Digital twin models are a crucial element for the digitalization of industrial plant maintenance: they enable virtual setup and validation of missions remotely before robots are deployed on-site, speeding up the installation of inspection robotics technology. In addition, real-time robot data fed into the digital twin enables operators to intervene quickly and preemptively.
ANYbotics – Accelerating deployment through digital twins
ANYmal supports the digitalization of operations through scanning and documenting 3D environment data as a digital twin for mission simulations, accelerated deployment, and advanced automated condition monitoring.
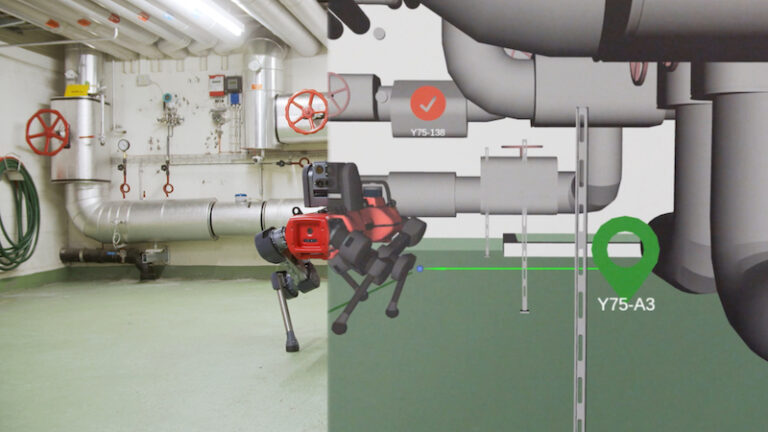
Using BASF’s facility CAD model, ANYbotics is able to pre-program and simulate robotic inspection missions.
- Maintenance Management System Integration
The inspection data must be integrated into your management systems for inspection robots to function as proper end-to-end solutions.
Integration with your maintenance management system, for example, allows you to:
- set up alerts
- react to detected anomalies early
- automate end-to-end workflows and preventive maintenance by triggering intervention actions.
Integration enables you to flexibly schedule routine and relevance-based monitoring, including on-demand, conditional, and spot inspections. Effectively integrating inspection data is most commonly achieved through application programming interfaces (APIs).
Software integration via APIs enables deep integration of robotic inspections into existing maintenance management systems.
In addition to transferring inspection reports and original files, many APIs offer the possibility of transferring sensor data in real-time.
Inspection robot APIs are typically based on the open source, standardized gRPC API and supported by a software development kit (SDK) in commonly used programming languages, e.g., C++ or Python. The connection to the robot from customer systems can be direct or managed through a robot data server for increased security and reliability. That server can be located on-site at the customer’s facility, in the customer’s cloud infrastructure, or optionally in the solution provider’s cloud infrastructure.
Integrating your inspection data via APIs facilitates consistent inspection data and analysis reports, as well as up-to-date information about the condition of your equipment and infrastructure.
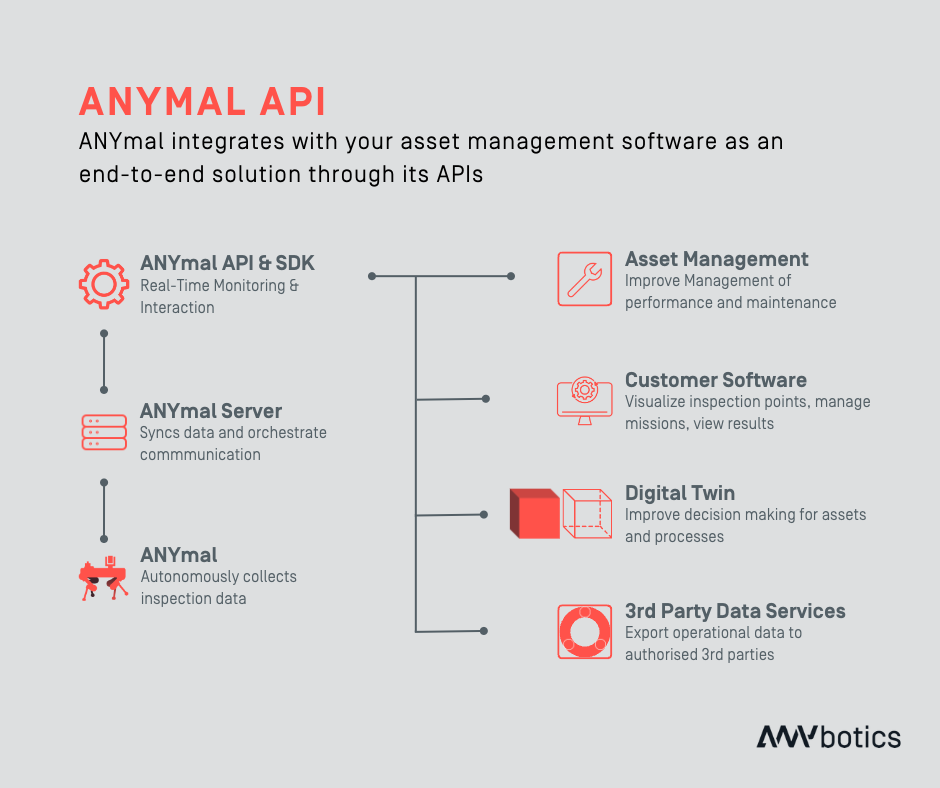
ANYmal – Integrating robots through APIs
ANYmal integrates with asset management software as an end-to-end solution through its APIs.
Data Interface and Analysis
Evaluate the best data interface to get the correct output from your inspections
Inspection robot solutions collect large amounts of data: evaluating the ideal data interface for your operations is essential to leveraging the best insights from the collected information.
Typical robotic inspection solutions provide one or multiple of the following data interfaces:
- User interface (UI): Direct access and interaction with the inspection results through the user interface of the robotic inspection solution. This interface can monitor the progress and results of inspection missions in real time (provided connectivity with the robot) and study the time series from a sequence of inspection runs.
- File exports: Inspection sensor data taken for points of interest includes, for example, images and video sequences for visual and thermal inspection, raw audio files for acoustic recordings, and point clouds for 3D asset scans. Access to raw data is ideal for further analysis and training of predictive models.
- Inspection reports: Complete inspection runs produce structured results, including details about the inspection analysis (e.g., the values read out), identifier, time, position, and other meta information. Providers often deliver inspection reports as PDF files for direct consumption and XML files for importing into other software.
Choose the best device for your operators to control the robot
High usability of inspection robots for non-experts is essential so that operators can set up, manage, and customize inspection jobs without calling in an integrator. Robot control devices and interfaces should fit into your daily work, meaning they should be rugged, waterproof, and able to be operated while wearing gloves.
Most robotic solutions offer a standard control device, and the software should ideally be device-independent and used from existing tablets and computers.
Leading robotic solutions provide a device-independent, intuitive user interface (UI) that allows a single operator to quickly and safely set up, review, and schedule autonomous or manual inspection missions and control the robot.
This reduces robot deployment time to less than a day and is recommended when scaling inspection robots for broad applications.
ANYbotics Workforce – Intuitive robot control from any device
The intuitive ANYbotics UI Workforce enables any plant personnel to operate ANYmal from any device. Workforce allows operators to set up and review missions, reducing ANYmal deployment time to a few hours.

The ANYbotics single-user tablet enables a single operator to set up complex inspection missions quickly.
Don’t Compromise on Safety
When choosing an inspection solution for industrial applications, it is crucial to address safety and security concerns to ensure comprehensive protection of sensitive data and operators and assets.
Here is a list of what you need to know:
Secure Your Data
An inspection robot generates and collects various data about itself, its operational environment, its missions, and the inspection points on its routes. This data is typically classified into one of two categories, which affects where the data is sent and processed.
- Environmental and Inspection data: Includes both data gathered in real-time from its onboard sensors used to understand and navigate its world (e.g., depth camera feeds and Lidar scans) as well as information used by the robot to perform its missions and the gathered inspection data, e.g., mission settings, 3D maps, navigation paths, and inspection results. While most data is discarded immediately, mission and inspection data can be processed and stored on the robot and forwarded to the operator’s computer or customer systems via the robot API. This means that the inspection output data should only be transmitted to the systems you define as the customer.
- Robot log data: Information about the robot’s activities and hardware and software performance (e.g., steps taken, battery cycles, software logs, inspection performance). This data is transmitted to the data server and the provider’s systems, where it is stored and processed. The solution provider usually uses this data to develop the robot solution further, improve its services, and better fulfill customer support requests.
Integrating data from mobile robotics solutions with your management system via APIs means that the data must be secure and meet your standards for data handling.. To avoid data security risks and business disruption due to data loss, integrity, authorization (e.g., GDPR in the EU), or intrusion (i.e., third-party hacking), the robotic platform and solution provider must have effective data security measures in place.
Ensure that the robotics solution provider complies with international information security management standards and implements security programs that ensure risk assessment and security controls. Also, ensure that the vendor communicates with its customers about incidents and threats, handles intermittent and unreliable connections without causing data breaches, and implements regular software and firmware updates to minimize security risks.
Prioritize Safety Considerations in Inspection Operations
Autonomous inspection robotics is a powerful, multidisciplinary technology. During the evaluation process, ensure that the solution meets your safety requirements by paying attention to these three aspects.
-
- Marks and Certification: The CE mark for products that meet EU health, safety, and environmental requirements and FCC certification for electronic components in the U.S. represent basic safety for people and the environment. IECEx (international) and ATEX (EU) are special certifications for equipment used in hazardous environments and potentially explosive atmospheres.
- Operational Safety: Mobile inspection robots move between plant equipment and physical objects, occasionally encountering workers. Full autonomy and extreme mobility are critical, meaning the robot can ‘see’, identify, and safely navigate your plant’s infrastructure. Leading inspection robots feature 360° vision, near-depth perception, and obstacle avoidance technology. In addition, these robots visibly communicate their operational status to the environment, e.g., through a red-green warning light system. They have multiple levels of accessible, certified emergency stop functionality and safety transport handles. Ensure operators do not need special equipment to physically or remotely shut down or move the robot.
To comprehensively address safety, best-in-class solution providers conduct on-site risk assessments in collaboration with end users. - User Training: Reputable robotic solution providers offer comprehensive online and on-site training to familiarize operators with key operating hazards, safety instructions, and emergency shutdown procedures. It is beneficial if they also have an online Learning Management System for retraining new joiners and a Master Operator module that allows your operators to train additional users in your organization independently.
ANYmal – Extending operator assistance
ANYmal and ANYmal X have several standard features that support operators and enable safe operation and transportation.

As businesses evaluate the prospect of integrating inspection robots into their operations, evaluating which task to automate and the robot capabilities needed to address the facility’s challenges becomes paramount to strike a delicate balance between innovation and responsibility.
By prioritizing data integrity and operator safety, industries can unlock the full potential of inspection robots while mitigating risks and upholding their commitment to operational excellence and employee well-being.
Start your robotic journey with ANYbotics
Get a glimpse of the value ANYmal can unlock
for your business with this 30-minute demo:


